LastPass Threat Intelligence, Mitigation, and Escalation (TIME) would like to alert our customers to an active phishing campaign that began on or around March 1, 2026. These phishing emails are being sent from several email addresses with various subject lines that look like forwarded internal messages about unauthorized access to individuals’ accounts. The known list of email addresses and subject lines can be found below.
This is an attempt on the part of a malicious actor to draw attention and generate urgency in the mind of the recipient, a common tactic for social engineering and phishing emails.
Campaign Overview
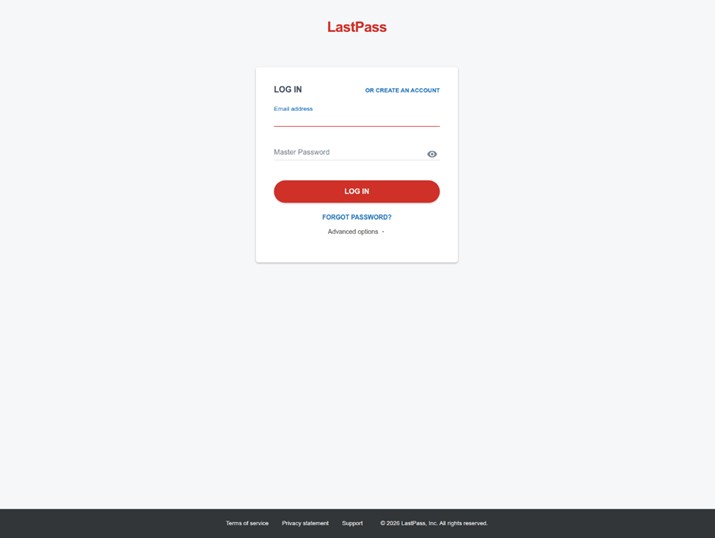
Attackers are forwarding fake email chains to make it appear as though another individual is trying to take unauthorized action on their LastPass account (i.e., export vault, full account recovery, new trusted device registered, etc.). Attackers use display name spoofing so that the name portion of the sender field is manipulated to impersonate LastPass, while the actual sending email address is unrelated. The attacker relies on the fact that many email clients (especially mobile) show only the display name, hiding the real sender address unless you expand it. The emails instruct targets to take some type of action (i.e., report suspicious activity, disconnect and lock vault, revoke device, etc.) if something looks off via provided links; these links then direct targets to fake SSO login pages via https[:]//verify-lastpass[.]com as the primary URL to collect users’ credentials (see below).
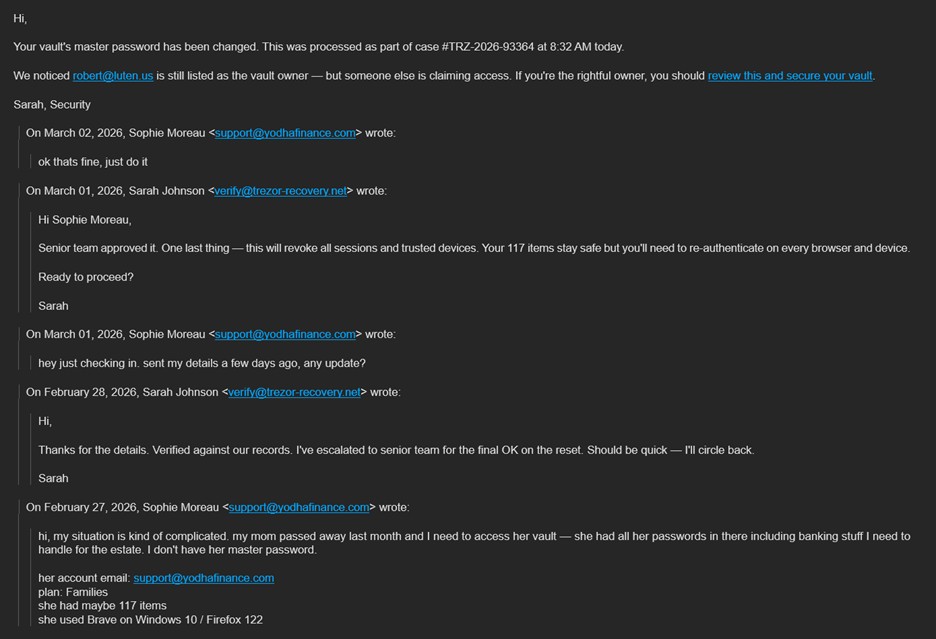
Body of Phishing Email Examples
The below images shows the fake correspondence and personas the threat actor included in emails to targets.

The image below displays the landing page that is a fake LastPass SSO login page.
What to do
Please remember that no one at LastPass will ever ask for your master password. Rest assured, we are working with our third-party partners to have these sites taken down as soon as possible. In the meantime, please take the appropriate precautions and, as always, if you are ever unsure whether a LastPass branded email is legitimate, submit it to abuse@lastpass.com. We would like to thank our customers who have already submitted this email for their vigilance and commitment to keeping our community secure.
Indicators of Compromise
Malicious URLs and associated IP addresses at time of publication:
At the center of the phishing chain is the domain https[:]//verify-lastpass[.]com. Most malicious links redirect to this domain, but the attackers generate many slightly modified versions by adding different trailing numbers. This lets them produce a large set of URLs that all resolve to the same phishing page.
- http[:]//url6163[.]hancochem[.]at/ls/click?upn=u001.zzKoeZ0KJwWxkAal-2BAEGAVZqjLZ-2Fi-2FvLLleyd0Mrg7G2tDUVYJx-2BwoTtA3VLtDQxDdnbMlSxrd48X2rqT3qjwA-3D-3D4tgO_sO-2BxZceWa0lJwX67h1R3P4373GdGx0dFRW1jYvRsz0zpAChfojQaxq2-2Bkg5LzfoxWNcUnJJfqqvxD7hQYHhN-2FI-2BPE3Xav0OFz-2FYfkten1SK5CpICpFh-2FePosONfhxOeAEuJOM6ptlTgkAjbq7cEdRaO5VlNg1llTkcEPO3z5AI0k9UpvVGTAzLPy2F5XkI2ozYLJlUrGPCZ-2F-2FB-2F1EZpCXWdDXN70q14FYvRYyMptdqWq4DhdemtpUyZ6Bmfl9JRinCHKTAB32JnuxqmjamSwTQ-3D-3D
- Redirects to https[:]//verify-lastpass[.]com/login?13
- Serving IP address: 172.67.200[.]82
- http[:]//email[.]mg[.]atomicminerals[.]ca/c/eJxszE1SwyAUAODTPJbM4_1AsmBRx8kJ3LgklKQ4IdUEO-rpvUAv8F1j8MLJmRJdCMRevARzizroUhafVa_jQPOsWgRLDqgJacloaiQkj4zOOUYJdhkppJFRWTxiURBsq0393mpudS9H2k6bk9nirffPE_gCNAFNc-12-wWa5KD3t3oBnn4yAvkH8OszAcjvwzr8mSOe3x9px9GRMNDLFwiuLdXN5nszj0j_AQAA__9YskAN?px7ik70&r=salud5i.cl&6
- Redirects to https[:]//verify-lastpass[.]com/login?14
- Serving IP address: 172.67.200[.]82
- https[:]//u48791940[.]ct[.]sendgrid[.]net/ls/click?upn=u001.ogpCsZrycFMCzfAiwPUWLmFsdkeI0MdEubFNgF3jgfqNQnFF7Sa4GacvI70clegZr1qhygt4EWt2YnP-2FiRMmaw-3D-3D5DWs_J8xRVsYbQP5fs7rIap1JbiZonM0buqGmCHMV-2BEiWHGtUxzu1WAuzO-2F7r3H3eREXp7XzUO3kzMmDj-2FdV-2F-2B4uWrIiJutCCPJ7YwmWdBDCht1WbPrgl1ya8BLo-2FkUCBo2UB47GOty9-2BpwLA0VbNvHAyb0HBKx8PxXXUIXmB-2BtJj5jHoGWLDU-2Fzhub-2F5uJgsSK4tOiGznacs1i4gOiTZYqi69QVYnU0ickYbRu9-2BQYsVwZ3Q-2B9-2Bb-2FidY2lMaojEQ4-2FdBB2GtXwZ6LtDo7p8V7d8WbA-3D-3D
- Redirects to https[:]//verify-lastpass[.]com/login?12
- Serving IP address: 104.21.21[.]204
- https[:]//u44889439[.]ct[.]sendgrid[.]net/ls/click?upn=u001.e-2BxTnSnQxOkncC20jNBuK6V4isKkl0XRDY4tivVdQQeqb6mLeZ9KZOFcqWpx39-2BnAE7mTDuZrA1c4CRwWnQJ87meMHF8VOjaNNH6wrLM3tM-3Dy3Wh_R1ZGbWCmLkaPZePSUmyQqgC1d5Ris5WwQ8-2BSDU4d1rdH8zGcPFFH4qlT8e5nEVVXDsX1sxkOVJGJxV2k3mwe-2FKfUVjKWBXPNmt-2BaH9C1gryEyEFxqdI02G0RJDIFrE6Nl4-2FW-2BO2bPI3S5k-2B-2FPb-2FQa5gviNQAk-2BIEXw6VHumTQbE6UHjUDbxJtHf1MonzbXBm5LIlU94C72GVqQpgivP2zmV1UE4e6UHNrQ0EU5kDakI-3D&t3fq0mvk&ref=deepai.cloud&4yo7x
- Redirects to https[:]//verify-lastpass[.]com/login?6
- Serving IP address: 52.102.103[.]4
- https[:]//u36129518[.]ct[.]sendgrid[.]net/ls/click?upn=u001.-2FOOkSPOOOLb9fpU79r0i5hEcjwfSQiTuVvlEgaG0hdHfvF0xmyV5ce3B4o7gGe0pUsHKDoF5ZYs1K2zEXVW9W-2F-2FdlazaOb4E5L8fdeTHrCk-3DEvrg_VBVoDhnIQxvCgpmdePRMMhkot7dkZlCJbRS3wbJOKNEIgFbdWxk02jlIRoEXWYDG-2Bu4QKAwbK0S7QyfOm51-2BaKSgcUhp9gIwP4JXcoWFOwS0EnG5t4esWxYDCzC0DArn6LAgJii-2F9ue3VcvjeqWEd6mhs3U83u8F7JNRQ94Icqdz466gV-2Fii3l-2B6SoPa9U0nLdiYN8Cfi381AtC6Kbro0T5nqaadfqtHC7xucIF3oGsjsHvz0ciYZ9bzxeP-2F6PpUrJifffYMQ4ROnoVh6uwC1g-3D-3D
- Redirects to https[:]//verify-lastpass[.]com/login?14
- Serving IP address: 104.21.21[.]204
- https[:]//u8790117[.]ct[.]sendgrid[.]net/ls/click?upn=u001.orExwStHYFDTU74GY1XA46huRVGl2xzICxrswbVNw6-2FtS6SAKtxwYwh83Ym-2FDWqHZcYQZJ-2FDSlAUAmoE8yFV0g-3D-3D6eeu_M-2Bd3xd1fzoxjC4kCStlaly-2FJia50cDswk4hS8HhdkZh4BaY2qwomdnOk9fz6pJQemyQsO5BiLR7Pcsr-2FFbAJeMmvGC-2FfI6pVbMaYAEYM-2B9xlijEYZ-2FdfUqJ5M4A6yAWTuHXacxHZX1hFEZJbjAKDus-2BqrDAGnOgWsIEabTDSyUaIqjQTLGTQikLOGwG5xj7wL3Wer5kxEXBuSuao3w4vxg-3D-3D&sq9fhcx&origin=fluxstore.io&i
- Redirects to https[:]//verify-lastpass[.]com/login?13
- Serving IP address: 52.102.103[.]12
- http[:]//email[.]mg[.]79resources[.]com/c/eJxkzU1OwzAQQOHTjJfR_DjjeOEFFcoJWCA2yLWdNlKsQuxUKqdHwJIDvPfl4P0YJzYlkHMsap2guQaenJRl0ZKTiBKmnEgJeUTKGhnNGhhZUZCIhAkHH_PZeTsVR8tiMYLFehmc30u7HXsqbUi3arZw7f2jgTwBz8Dzee3D9gCebX99e4knkDlV-2VlA9aj1_e_GOT5_wxY24PuZg-H-JFF0QGfSvv8sS81rtsveQ_8HQAA__-ytUM_?ci&tag=yodhafinance.com&vtzlng
- Redirects to https[:]//verify-lastpass[.]com/login?11
- Serving IP address: 104.21.21[.]204
- http[:]//email[.]mg[.]redlakegold[.]ca/c/eJxky0FOxSAQANDTDEsCw3ToX7DQmK69Agy0JR_8TYsm9fQewAO8HCinPKEqwXqPjokfpPZgKGUxiT3LTDKjnfL6KKvEKOQFk6oBDbJxxlrrrCNNzgoyz1OcVo6-AJm-6bPkFp9le7WsJaoW9jGOC9wb4AK4pDp0uwEXOsvv8XmDW-QA5AHu478-w12uXr9k_-7PagHfOQGZrcfatLy6-gn4FwAA__9PZD7G?g2fk3tf3&tag=bebran.com&bd
- Redirects to https[:]//verify-lastpass[.]com/login?6
- Serving IP address: 52.102.103[.]50
- http://email.mg.redlakegold.ca/c/eJxky0FOxSAQANDTDEsCw3ToX7DQmK69Agy0JR_8TYsm9fQewAO8HCinPKEqwXqPjokfpPZgKGUxiT3LTDKjnfL6KKvEKOQFk6oBDbJxxlrrrCNNzgoyz1OcVo6-AJm-6bPkFp9le7WsJaoW9jGOC9wb4AK4pDp0uwEXOsvv8XmDW-QA5AHu478-w12uXr9k_-7PagHfOQGZrcfatLy6-gn4FwAA__9PZD7G?bwu71&utm_source=bebran.com&2nxq14
- Redirects to https[:]//verify-lastpass[.]com/login?6
- Serving IP address: 104.21.21[.]204
- http[:]//email[.]mg[.]bedfordmetals[.]com/c/eJxszUtuwyAQANDTDEuL-TCGBYtWFfcwv8QSKGniWM3tK3XdC7xXoy_sVjIt4roSq6hXc43StInNnXLDECg7rtVTdyVj7pjZ7JEsqWWLiIykS5cSmvMSNtfRFwGx87LkVvvtUWc7tvFcym2aEa_HcX8CfwAloJT3YxlvoCRDbNo34PRd5vvn7EB6An_9pwDp3Tzii4MjVrsCfb4YxF7mto-_5oz0GwAA__-9fkCb?8v&v=itpbusa.com&jat472k
- Redirects to https[:]//verify-lastpass[.]com/login?5
- Serving IP address: 104.21.21[.]204
- http[:]//email[.]mg[.]bedfordmetals[.]com/c/eJxszUtuwyAQANDTDEuL-TCGBYtWFfcwv8QSKGniWM3tK3XdC7xXoy_sVjIt4roSq6hXc43StInNnXLDECg7rtVTdyVj7pjZ7JEsqWWLiIykS5cSmvMSNtfRFwGx87LkVvvtUWc7tvFcym2aEa_HcX8CfwAloJT3YxlvoCRDbNo34PRd5vvn7EB6An_9pwDp3Tzii4MjVrsCfb4YxF7mto-_5oz0GwAA__-9fkCb?8v&v=itpbusa.com&jat472k
- Redirects to https[:]//verify-lastpass[.]com/login?5
- Serving IP address: 172.67.200[.]82
Sender email information:
From:
- office@hancochem.at
- admin@salud5i.cl
- no_reply@remstal-praxis.de
- demo@fluxstore.io
- no_reply@kreducationsa.com
- support@yodhafinance.com
- hr@bebran.com
- info@itpbusa.com
Subjects:
- Re: the details
- Re: pending approval
- Re: Access request pending
- Re: FYI
- RE: sign-in — TRZ-2302300
- Fwd: Re: your request
- Re: credential download




